Online forms are everywhere. They’re used for appointments, deliveries, subscriptions, job applications, travel bookings, and account creation. The problem is that forms look harmless. A few fields, a publish button, perhaps a checkbox or two. But at the back of that easy format is a switch of private data, and as soon as it leaves the screen, manage will become tougher to track.
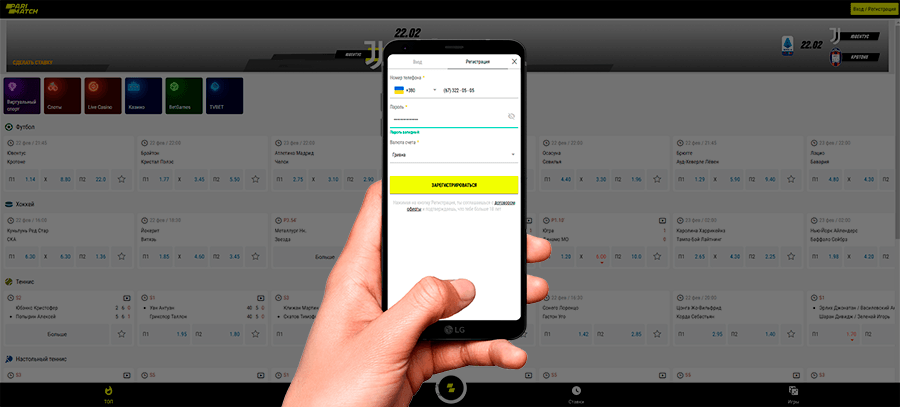
That’s why any registration flow, whether it’s a basic newsletter or something more structured like parimatch sign up, should trigger the same mindset: verify the page, minimize what’s shared, and confirm the platform’s handling of identity and payment data before entering anything sensitive.
The first rule: a form is only as safe as the site hosting it
People regularly consciousness at the questions within the form, however the actual hazard is the surroundings round it. A clean-searching web page can nonetheless be a clone, a redirect chain, or a phishing setup.
Quick checks that take seconds:
- confirm the domain spelling matches the official site exactly
- avoid registration links received through random messages or popups
- look for a secure connection (HTTPS) and a locked icon, then click it to view certificate details
- watch for unusual subdomains or long, messy URLs that look auto-generated
If anything feels “off,” closing the tab is the smartest security move.
Share the minimum, not the maximum
Many forms ask for more than they need because companies want richer profiles. That doesn’t mean users should comply automatically.
A practical approach:
- if a field is optional, treat it as optional
- avoid entering extra identifiers (secondary phone, alternate email) unless necessary
- do not provide address details unless the service truly requires delivery or identity verification
- never upload documents until the platform’s legitimacy is confirmed
The less data shared, the less damage possible if something goes wrong.
Red flags inside the form itself
Some warning signs appear in the questions and flows.
Be cautious when a form:
- requests banking information in plain fields rather than secure payment steps
- asks for SMS codes repeatedly without clear reason
- demands access to contacts or device storage to “continue”
- forces document uploads immediately, before any account settings exist
- uses urgency language such as limited access or account will be blocked
Legitimate systems can nevertheless have terrible UX, however competitive strain methods are a conventional phishing tool.
Password hygiene: the easiest win with the biggest impact
Weak passwords stay one of the maximum not unusualplace methods bills get compromised. The repair isn’t always complicated, simply boring.
Safer account basics:
- use a unique password for each site
- prefer long passphrases over clever short passwords
- store credentials in a password manager instead of reusing variations
- enable two-factor authentication when available
If a form rejects strong passwords or limits length aggressively, that’s not “security.” It’s outdated engineering.
Understand what happens after you hit submit
A trustworthy registration flow doesn’t end at “success.” It provides clarity.
Signs of a responsible platform:
- verification emails or confirmations that match the domain
- an account area with privacy and security settings
- the ability to review, edit, or delete data where applicable
- clear support access for account issues
If the process ends abruptly with no confirmations, no account controls, and no settings, it’s worth questioning what was just shared.
Public Wi-Fi and shared devices: the silent risk layer
Even a legitimate website can become risky if the environment is unsafe.
Common mistakes:
- signing up on public Wi-Fi without a VPN
- using shared computers without private browsing
- leaving sessions logged in on borrowed devices
- saving passwords in public browsers
On shared devices, always log out, clear session data, and avoid storing credentials. It sounds basic, but it prevents a surprising number of real-world issues.
A simple checklist before submitting any online form
A fast, repeatable routine helps:
- verify the domain and secure connection
- check for pressure tactics and strange permission requests
- share only what’s required
- use a unique strong password
- enable 2FA if offered
- confirm there’s a real account dashboard and support path afterward
Most data problems don’t start with advanced hacking. They start with rushing through a form on the wrong page. Online registration should feel easy. But it should never be mindless.


Leave a Comment